Event ID 4625 – The best method for boosting domain security against failed logon attempts.
A failed logon attempt is indicated by the event with the ID 4625 in the Windows Security Log. When a user enters improper credentials, such as a bad username or password, or when the user account is locked out or disabled, this event is triggered.
This event can be used to keep track of unsuccessful logon attempts and spot any account-based brute-force assaults. Additionally, it can aid in locating compromised user accounts or potential insider threats.
The event contains details regarding the user account, the origin of the login attempt (such as a local or distant computer), the time of the attempt, and the cause of the failure. This event can be used by security administrators to look into security occurrences, find security weaknesses, and take the necessary steps to reduce security risks.
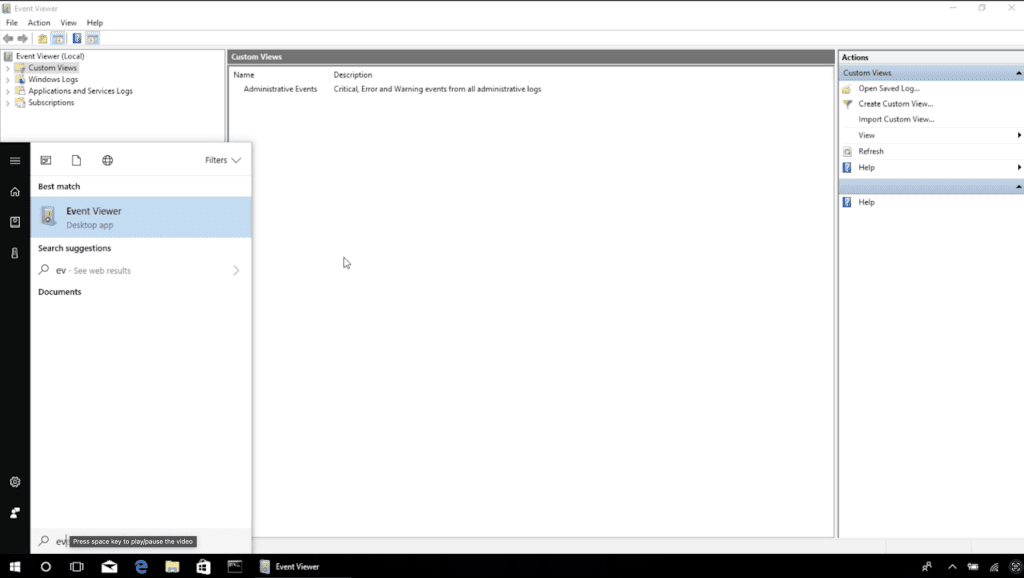
Security administrators have several options for looking into security issues using Windows Security Log Event ID 4625:
How to spot probable brute-force attacks: A brute-force assault may be underway if several failed logon attempts occur quickly from the same source IP address or user account. Security administrators can look into these logon attempts to identify the assault’s origin and take the necessary countermeasures to stop or lessen the attack.
Identify compromised user accounts: If failed logon attempts are coming from a user account that has never been used or that belongs to a person who is not currently employed by the company, this may be a sign that the account has been compromised. Security administrators can look into these logon attempts to see if the account has been compromised and then take the necessary actions to disable the account or reset the password.
How to spot insider threats: Failed logon attempts from a user account that belongs to an employee who is still working for the company may be a sign of an insider threat.
Monitor security compliance: Security administrators can utilise Event ID 4625 to track unsuccessful logon attempts to privileged accounts or accounts with elevated access in order to monitor security compliance. By doing so, it will be possible to spot any security policy infractions and check that those policies are being followed.
Eventcode 4625 PowerShell Script
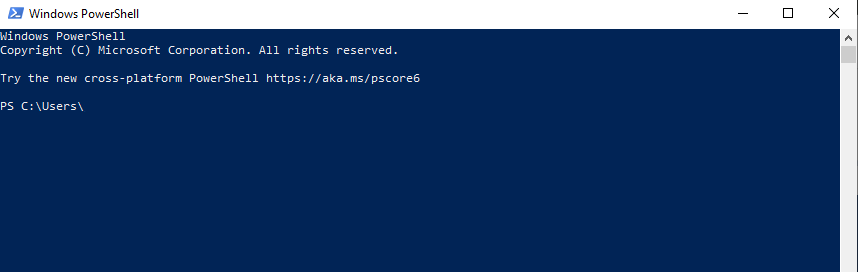
We will now show you an example script which returns all unsuccessful logon attempts that have occurred over the last 24 hours that match Event ID 4625 from the Security Log. It gathers and keeps in a custom object the time, user account, source IP address, and cause for the failure. The script can be altered to save the data in a database or flat file for additional analysis.
To access the Security Log, keep in mind that you might need to run this script with elevated rights.
# Set the start time and end time for the log query (in this case, the last 24 hours)
$StartTime = (Get-Date).AddDays(-1)
$EndTime = Get-Date
# Set the filter to only retrieve Event ID 4625 (Failed Logon)
$Filter = @{
LogName = 'Security'
ID = 4625
StartTime = $StartTime
EndTime = $EndTime
}
# Retrieve the log entries that match the filter
$LogEntries = Get-WinEvent -FilterHashtable $Filter
# Loop through each log entry and extract the relevant information
$FailedLogins = foreach ($LogEntry in $LogEntries) {
# Extract the time, user account, source IP address, and reason for the failure
$Time = $LogEntry.TimeCreated
$User = $LogEntry.Properties[5].Value
$SourceIP = $LogEntry.Properties[18].Value
$FailureReason = $LogEntry.Properties[8].Value
# Create a custom object to store the information
[PSCustomObject]@{
Time = $Time
User = $User
SourceIP = $SourceIP
FailureReason = $FailureReason
}
}
# Display the failed login attempts
$FailedLogins